You get the following error message in the LDAP event log:
Id : 1220
Message : LDAP over Secure Sockets Layer (SSL) will be unavailable at this time because the server was unable to obtain a certificate.
Additional Data
Error value:
8009030e No credentials are available in the security package

The reason
It is always a certificate problem.
However, there can be multiple reasons behind the same error message,
and all the following requirement have to be met.
Certificate requirements
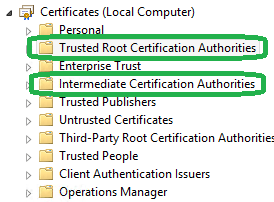
- The LDAPS certificate is located in the
Local Computer‘s Personal certificate store (programmatically known as the
computer’s MY certificate store).
Follow this link to see different ways to import a certificate into the Local
Computer’s store

- A private key that matches the certificate is present in the Local Computer’s store and is correctly associated
with the certificate.
- The private key strong protection has to be disabled.
KeyProtection = NCRYPT_UI_NO_PROTCTION_FLAG

- The Enhanced Key Usage extension includes the Server Authentication (1.3.6.1.5.5.7.3.1) object identifier (also
known as OID).[EnhancedKeyUsageExtension] OID=1.3.6.1.5.5.7.3.1 ; Server Authentication

- The certificate was issued by a CA that the domain controller and
the LDAPS clients trust. Trust is
established by configuring the clients and the server to trust the root CA
to which the issuing CA chains.
- You must use the Schannel CSP to generate the key.
ProviderName = "Microsoft RSA SChannel Cryptographic Provider"

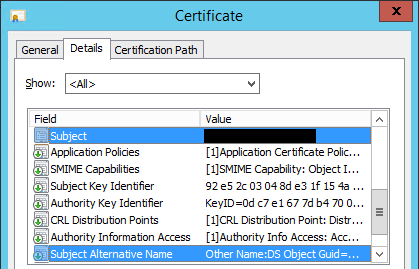
- The Active Directory fully qualified domain name of the domain controller (for example, DC01.DOMAIN.COM) must
appear in one of the following places:- The CN in the Subject field.
- DNS entry in the Subject Alternative Name extension.
Note
This last requirement was the problem in my case.
I falsely assumed that having the DNS entry in
the Subject field was sufficient.
In fact, it must be both in the subject and also in the SAN
field. Furthermore, it must be the first one in the list.

More about
How
to enable LDAP over SSL with a third-party certification authority (KB321051)

LikeLike
Hi, I am facing similar issue, but I struggle to follow this explanation. Can you provide a little more details please?
How do I change The Enhanced Key Usage?
How do I use Schannel CSP to generate the key?
I only know how to import cert in mmc, but I don’t know how to access the other dialogs in your screenshots.
Thanks
LikeLike
Hi Mike!
You must open the certificate template console.
See my other post: https://itluke.online/2017/12/05/how-to-open-the-certificate-templates-console/
Then just use the same settings as on the screenshots.
1 “Cryptography” tab
2 Select “Determined by CSP” (Channel Service Provider) as Algorithm name
3 Select “Request must use one of these providers”
4 Check “Microsoft RSA SChannel Service Provider”
1 “Extension” tab
2 Select “Application policies”
3 Click the “Edit” button
4 Select “Server authentication”
Have a nice day Mike!
LikeLike
Thanks!
LikeLike
Hey Luke,
Thank you so much for your post. It saved me a lot of headache. My problem was also DNS alternate names. Really appreciate the posting.
Jay Kulsh
LikeLiked by 1 person